Self-custody wallets give poker players direct control over private keys, eliminating reliance on exchange or platform custody. This control comes with absolute responsibility: lost keys mean lost funds with no recovery mechanism. Understanding custody models is fundamental to cryptocurrency poker strategy, particularly for players managing meaningful bankroll allocations in crypto.
The distinction matters because custodial and non-custodial wallets carry inverse risk profiles. Exchange wallets expose you to platform risk—hacks, insolvency, regulatory seizure, withdrawal freezes. Self-custody wallets expose you to operational risk—key loss, physical theft, user error. Neither model is universally superior. The right choice depends on your security knowledge, fund allocation, and how frequently you need access to those funds.
This guide breaks down custody architecture, explains the technical differences between wallet types, and outlines the operational security practices experienced players use to protect Bitcoin and other cryptocurrency bankrolls.

Understanding Custody in Crypto Poker
Custody refers to who controls the private keys associated with a cryptocurrency address. Private keys are cryptographic strings that authorize transactions—whoever holds the private key controls the funds at that address, unconditionally. There is no customer service escalation, no chargeback, and no account recovery if keys are lost or compromised.
In traditional finance, custody is handled by institutions. Banks, brokerages, and payment processors hold assets on your behalf, with regulatory protections and recovery mechanisms built in. Crypto inverts this model: self-custody means you are the institution. You assume full responsibility for key generation, storage, backup, and operational security.
For poker players, custody decisions affect three practical areas: how quickly you can deposit, how securely funds are stored between sessions, and what happens if something goes wrong. Players who understand custody architecture make better decisions across all three dimensions.
Wallet Types and Their Custody Models
Not all wallets are equal in terms of custody. The spectrum runs from fully custodial (exchange wallets) to fully self-custodial (hardware wallets and multi-sig setups), with software wallets occupying a middle ground depending on implementation.
Custodial Wallets (Exchange-Held)
When you hold funds on a centralized exchange, the exchange controls the private keys. You have a balance in their database, not actual on-chain custody. This is operationally convenient—deposits and withdrawals are fast, no key management required—but it introduces counterparty risk. If the exchange is hacked, becomes insolvent, or faces regulatory action, your funds may be inaccessible or lost entirely. The 2022 FTX collapse demonstrated this risk concretely: users with exchange balances lost access to funds they believed were theirs.
Software Wallets (Self-Custodial)
Software wallets (MetaMask, Electrum, Trust Wallet, etc.) generate and store private keys on your device. You control the keys, but they exist in an internet-connected environment. This creates attack surface: malware, phishing, compromised browser extensions, and clipboard hijacking can all expose keys stored in software wallets. Software wallets are appropriate for active amounts—funds needed for regular deposits—but not for long-term storage of significant balances.

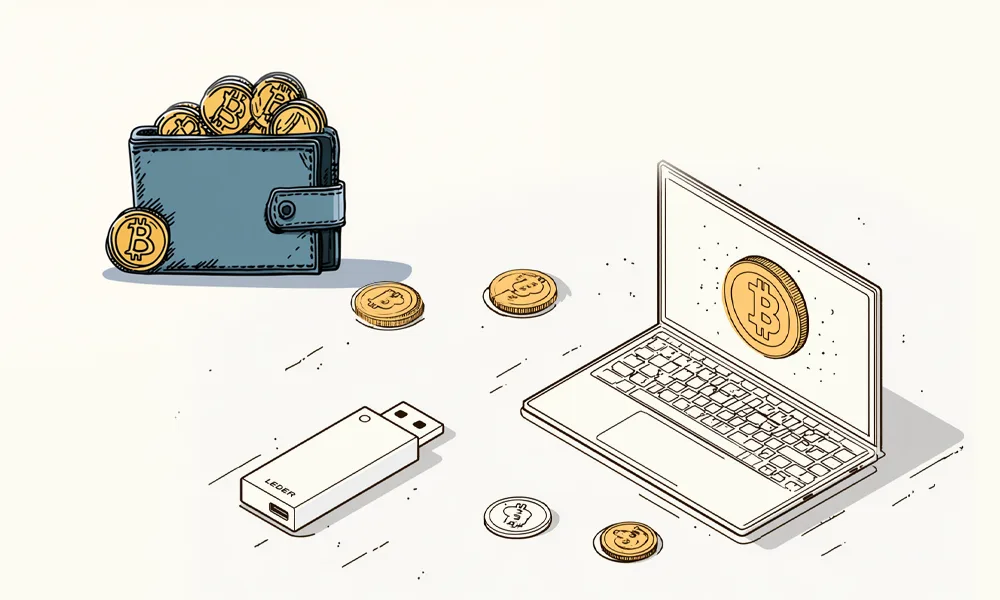
Hardware Wallets (Self-Custodial, Offline)
Hardware wallets (Ledger, Trezor, Coldcard) store private keys in a dedicated secure element, physically isolated from internet connectivity. Transaction signing occurs on the device itself—private keys never leave the hardware. This eliminates remote attack vectors entirely. The remaining risks are physical: device loss, theft, or hardware failure. Hardware wallets are the standard recommendation for storing crypto balances that exceed your comfort threshold for software wallet exposure.
Multi-Signature Wallets
Multi-sig wallets require multiple private keys to authorize a transaction—commonly 2-of-3 or 3-of-5 configurations. No single key compromise can move funds. This architecture eliminates the single point of failure present in standard single-key wallets. The trade-off is operational complexity: each transaction requires coordination across multiple signing devices or parties. Multi-sig is used by players and organizations managing balances where single-key compromise would represent significant loss relative to their overall holdings.
| Wallet Type | Custody Model | Key Storage | Primary Risk | Best Use Case |
|---|---|---|---|---|
| Exchange Wallet | Custodial | Platform-controlled | Platform insolvency / hack | Active trading, frequent deposits |
| Software Wallet | Self-custodial | Device encrypted storage | Malware, device compromise | Regular access, medium amounts |
| Hardware Wallet | Self-custodial | Offline secure element | Physical theft, user error | Long-term storage, large amounts |
| Multi-Sig Wallet | Self-custodial | Distributed keys (2-of-3, 3-of-5) | Key coordination complexity | Maximum security, high-value holdings |
Choosing between these models requires honest assessment of your technical capability, access frequency, and the value at risk. Most active poker players use a layered approach rather than a single wallet type.

What Self-Custody Means in Practice for Poker Players
Self-custody in a poker context means your bankroll exists on-chain at an address you control, rather than as a balance in a platform database. When you’re ready to play, you initiate a deposit from your self-custody wallet to ACR Poker’s deposit address. When you withdraw, funds return to your wallet. The poker site acts as a temporary custodian only during active play—your long-term storage remains under your control.
This model creates a clear operational separation: funds on-site are at platform risk (small, active playing balance), funds in self-custody are at personal operational risk (larger reserve balance). Managing this separation deliberately is what distinguishes players who think systematically about crypto processing from those who don’t.
Common Self-Custody Mistakes Players Make
- Storing seed phrases digitally—photographing or emailing a 12-24 word seed phrase exposes it to cloud storage breaches and device compromise; seed phrases must be stored on physical media only
- Using a single hardware wallet without a backup seed phrase stored separately—device failure or loss without a backup means permanent fund loss
- Generating wallet addresses on internet-connected devices when high security is required—true cold storage requires air-gapped key generation
- Reusing deposit addresses across multiple sessions—address reuse reduces privacy and can link transaction history to your identity through chain analysis

Seed Phrases, Key Derivation, and Backup Architecture
How Seed Phrases Work
Most modern wallets use BIP-39 seed phrases: 12 or 24 words that encode the master private key for an HD (hierarchical deterministic) wallet. From this single seed, the wallet derives unlimited child addresses across multiple blockchains. This means one seed phrase backs up your entire wallet—all addresses, all chains, all balances—but it also means that compromising the seed compromises everything derived from it.
Backup Storage Requirements
The seed phrase is the ultimate recovery mechanism and the ultimate attack vector simultaneously. Physical backup on paper or metal is the baseline requirement. Paper is vulnerable to fire and water damage; metal seed phrase storage (stamped steel plates) survives physical disasters. Multiple copies stored in geographically separate secure locations reduce single-location risk. No copy should exist in digital form under any circumstances—cloud storage, email, password managers, and screenshots all create exploitable exposure.
Passphrase Extension (25th Word)
BIP-39 supports an optional passphrase—sometimes called the “25th word”—that creates a distinct wallet from the same seed phrase. If an attacker finds your seed phrase, the passphrase prevents access to the passphrase-protected wallet. This two-factor approach separates physical possession of the seed from knowledge of the passphrase. It introduces its own complexity: if the passphrase is forgotten, funds in that wallet are permanently inaccessible.
Real-World Scenario: Setting Up a Self-Custody Poker Bankroll
A player decides to transition 80% of their poker bankroll from exchange custody to self-custody, maintaining a smaller active balance for frequent deposits.
- Total bankroll: Divided into active portion (20%) kept in software wallet for regular ACR Poker deposits, reserve portion (80%) moved to hardware wallet cold storage
- Hardware wallet setup: Key generation performed offline, seed phrase backed up to two stamped steel plates stored in separate physical locations
- Deposit workflow: Active software wallet receives scheduled transfers from hardware wallet during low-fee windows; deposits to ACR Poker initiated from software wallet only
- Withdrawal workflow: Winnings accumulate in software wallet; periodic consolidation transfers to hardware wallet during scheduled rebalancing
The Technical Process
The player connects the hardware wallet to a clean device (no browser extensions, no unknown software) to initiate the cold-to-hot transfer. They verify the destination software wallet address character-by-character before confirming on the hardware device. The hardware wallet signs the transaction internally; the private key never leaves the device. Transfer confirms on-chain in 2-3 confirmations. Download the ACR Poker software and initiate deposits from the software wallet only—never directly from cold storage.
The Outcome
The active software wallet holds enough for 2-3 sessions without requiring cold storage access, reducing hardware wallet exposure frequency. The reserve in cold storage is only accessed for scheduled refills—typically monthly or when the active balance drops below a predetermined threshold relative to their bankroll. This architecture limits attack surface to the software wallet (lower value) while securing the majority of funds behind hardware-level key isolation.
How Professional Players Manage Self-Custody
Experienced self-custody users treat key management as a formal operational procedure rather than an afterthought. They document their wallet architecture—what addresses hold what, where seeds are stored, what the recovery procedure is—and store that documentation securely. This matters not just for personal recovery but for estate planning: crypto held in self-custody with no documented recovery path is permanently inaccessible upon death or incapacitation.
Technical Risk Management
Professionals segment their holdings across multiple wallets with clearly defined purposes: a hot wallet for active deposits, a warm wallet for medium-term reserves accessible within hours, and cold storage for long-term holdings requiring maximum security. They never store more in hot wallets than they’re prepared to lose to a software compromise. They also verify wallet software against official checksums before installation and use dedicated devices for high-value signing operations.
System Optimization
Advanced players use hardware wallet address verification—confirming the receive address displayed on the hardware wallet screen matches what appears on the computer—to defend against address substitution malware. They enable passphrase protection on hardware wallets holding significant balances. They test their recovery process by restoring from seed phrase to a secondary device before committing large funds, confirming the backup actually works before depending on it.
Self-Custody and Protocol Evolution
The self-custody model is likely to become both easier and more important as crypto poker adoption grows. Easier because wallet UX is improving rapidly—hardware wallets now have companion apps that simplify transaction management without exposing keys. More important because as regulatory scrutiny of exchanges increases, custodial risk profiles may shift. Players who have established self-custody practices before regulatory changes are better positioned than those dependent on platform custody.
Multi-party computation (MPC) wallets represent an emerging middle ground: they distribute key shards across multiple parties or devices without requiring traditional multi-sig coordination overhead. These systems maintain self-custody principles while reducing the operational friction of multi-sig setups. For poker players, this means future wallet options will likely offer hardware-equivalent security with software-equivalent usability—though the underlying principle remains unchanged: control of keys equals control of funds.
Frequently Asked Questions
What is the difference between a private key and a seed phrase?
A private key controls a single address. A seed phrase (12-24 words, BIP-39 standard) is a master backup that derives all private keys in an HD wallet—every address across every blockchain the wallet supports. Losing the seed phrase while losing device access means permanent loss of all funds. The seed phrase is the more critical backup to protect.
Can a poker site access funds in my self-custody wallet?
No. Once funds are in your self-custody wallet, only you can authorize transactions—by signing with your private key. The poker site has no access to addresses you control. Funds are only at site custody risk during the period they reside in your on-site balance. Withdrawing funds to your self-custody wallet removes them from platform risk entirely.
Is self-custody safe for players who aren’t technically experienced?
Self-custody is safe when operational procedures are followed correctly, regardless of technical background. The primary risks are procedural—storing seeds incorrectly, skipping address verification, or losing backup copies—not technical. Users who follow hardware wallet setup guides carefully and maintain physical seed backups can manage self-custody safely. The risk isn’t complexity; it’s complacency with backup and verification steps.
What happens to self-custody funds if my hardware wallet breaks?
The device is replaceable; the seed phrase is not. Any hardware wallet supporting the same BIP-39 standard can restore your wallet from the seed phrase—even a different brand. Hardware failure with a secure seed backup means a new device purchase and a restore process, not fund loss. This is why seed phrase backup is more critical than device protection.
Should I deposit to ACR Poker directly from a hardware wallet?
Not recommended for regular use. Hardware wallets are optimized for infrequent, high-security transfers—not frequent small deposits. The preferred approach is maintaining a funded software wallet as an intermediate hot wallet. Transfer from cold storage to the software wallet periodically, then deposit to the poker site from the software wallet. This limits cold storage exposure frequency while maintaining operational flexibility.
What is address verification and why does it matter?
Address verification means confirming the destination address shown on your computer matches what your hardware wallet displays on its own screen. Address substitution malware can silently replace copied addresses with attacker-controlled ones. Hardware wallets display the true signing destination on a tamper-resistant screen. Always verify the full address on the hardware device before confirming any transaction—a partial check is insufficient.